- Authorities trace the theft and laundering of cryptocurrencies related to North Korea.
- The OXT firm performs an analysis of the transactions involved and reveals the laundering methods.
A new report delves into the methods used by hackers affiliated with North Korea to launder stolen cryptocurrencies from their victims, primarily from crypto exchanges.
Based on the analysis of civil lawsuit number 20-606, filed on March 2 before the United States judicial authorities, the OXT firm analyzed the movements and transactions of Bitcoin and other networks, discovering the methods used by cybercriminals to hide their illegitimate transactions in cryptocurrencies.
In this US legal process, two Chinese citizens (Tian Yinyin and Li Jiadong) are accused of laundering related money stemming from the hacking of South Korean crypto exchanges and other cyber attacks.
According to the OXT report, the criminals managed to withdraw a total of USD 67.3 million dollars by depositing them in Chinese banks, in addition to 1.5 million in iTunes gift cards, using the the peer-to-peer exchange service of Paxful to acquire them.
Although the complaint does not link these two hackers to the Lazarus group, the infamous cybercriminal organization that has been linked to the North Korean government, a recent OFAC (Office of Overseas Asset Control) provision does include the addresses of the case on their sanctioned list.
The hacking of virtual currency exchange houses and related money laundering for the benefit of North Korea represents a serious threat to the security of the global financial system. These charges should serve as a reminder that law enforcement, through their allies and collaborators, will uncover illegal activities around the world, prosecute those responsible for them, and confiscate illicit funds even when they are virtual assets.
Timothy J. Shea, District of Columbia Attorney
Although the court document does not indicate the name of the exchange houses, OXT does mention these companies. OXT contrasts the publicly known information with the data included in the lawsuit to find the possible names of the victims.

The two subjects are accused of laundering thousands of BTC and ETH in three phases. In the first of these phases, they implemented a Peeling structure, a money laundering method that, in combination with CoinJoin, makes it difficult to trace their perpetrators, but which must be carried out with certain precautionary measures to make it successful.
The Peeling is a process of transactions concealment that, starting from a main address, each transaction of the cycle has two outputs: one of smaller size towards a third direction (property of the initial issuer) and another of large size (almost all the amount) as change to the issuer of the transaction, explains OXT, who have noticed this pattern of transactions since the Mt. Gox case.
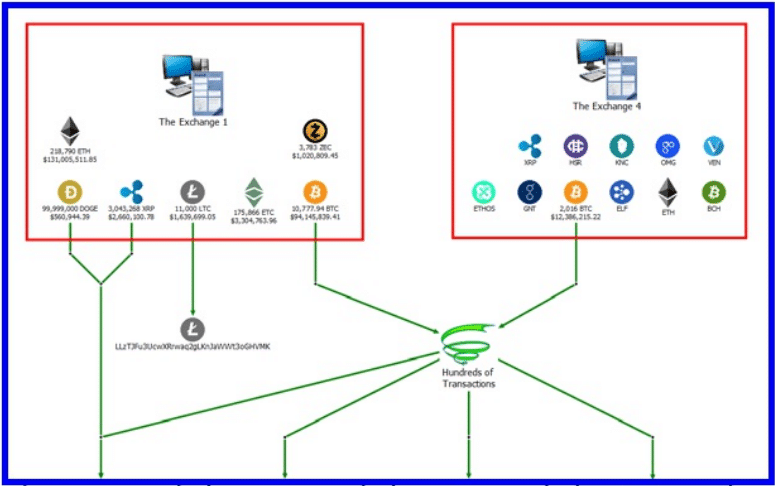
In the second phase, cybercriminals deposited their funds at crypto exchange that do not implement KYC (Know Your Customer, Know Your Customer) policies. Retaining the funds for a certain time in the custody of these exchange houses helps to camouflage the funds with those of other users, making it difficult to track them.
In 2018, the hackers of the Bithumb exchange house deposited about 2000 stolen BTCs in YoBit, an exchange house established in Russia and also listed in the OXT report.
In the third phase, they withdrew funds to sites that offer the exchange of cryptocurrencies for national fiat currencies, although these services mostly require user identity authentication. At this point, the funds would have been clean to withdraw permanently, because in the second phase the relationship points with the stolen funds would be broken.
In mid-2019, the UN assured that hackers affiliated with North Korea have obtained up to USD 2 billion in cyber attacks against financial institutions and cryptocurrency exchange houses, in a report that by then accounted for 35 cases worldwide.
In 2019 there were up to $282 million in cryptocurrencies lost to cyber attacks, according to the firm Chainalisys, which also highlights how hackers have improved their methods to mislead transaction tracking, although it is not impossible if the trackers have significant computing power.
Toxic Recall, one wrong step betrays criminals
OTX defines “Toxic Recall” as a method that allows a cycle of money laundering or a series of transactions to be traced through small “toxic” traces that they gradually leave, they explain in a report available on their website, published at the beginning this month, titled Toxic Recall Attack – Unwinding JoinMarket Case Study.
This procedure was implemented in the tracking of 445 BTCs reported as stolen by a Reddit user in 2015. The user has not yet been located, despite several attempts to contact him and that the BTC in question are practically unrecoverable, according to OXT. .
According to OTX, the initial user of a CoinJoin process can be traced if the participating outputs throughout the process had previously been used. By following the “toxic” traces, they can completely de-anonymize a user.
By analyzing the inputs and outputs that are similar in terms of the amount of funds they have, researchers can infer which ones correspond to each other, they say. But also, highlighting the unmixed exits, they can realize the path and final destination of the coins in question, which would dictate the progress of the investigation.
In this case, they specify, CoinJoins made with the JoinMarket client were taken into account, although this tracking method is applicable to CoinJoins made from Wasabi wallets as well. They also point out that the findings of this research are being used to reinforce the Whirlpool protocol of the Samourai portfolio, a portfolio focused on the privacy of its users.
Because cyber criminals use privacy tools like CoinJoin, the authorities have been interested in learning how it works. This was revealed by a recent internal report by Europol, which assesses the difficulty that the Wasabi portfolio entails in tracing illegal transactions by this police entity.